...
System Configuration
...
System Administration
...
Authentication
...
Defect Tracking Setup
...
Customizations
...
About Zephyr
Zephyr
...
Authentication
Zephyr provides multiple options in which users can be authenticated when they log into the system. This is referred to as Primary Authentication.
Primary Authentication are:
Internal
LDAP
Atlassian Crowd
WebService
Single Sign-
...
on
Secondary Authentication: If LDAP/Crowd/Webservice is being used for primary authentication and certain temporary/migrant/external users that are not in those systems need access to Zephyr, the secondary authentication option can be turned on to allow that.
| Warning |
|---|
Please note that this process is only for authentication and not for synchronizing user information with these systems. |
Primary Authentication
...
1. InternalAnchor Internal Internal
Administrators can leave the selection at 'Internal' to use the native Zephyr authentication system. The user ID and passwords that are stored in the User Setup section are used to authenticate users.
- This is the default option.
- Users can reset their own passwords by clicking on the 'Profile' link in the top right corner of their interface.
| Anchor | ||||
|---|---|---|---|---|
|
If your organization is using an LDAP server for authentication, the Zephyr Server can be setup to authenticate users using LDAP.
...
| Info | ||
|---|---|---|
| ||
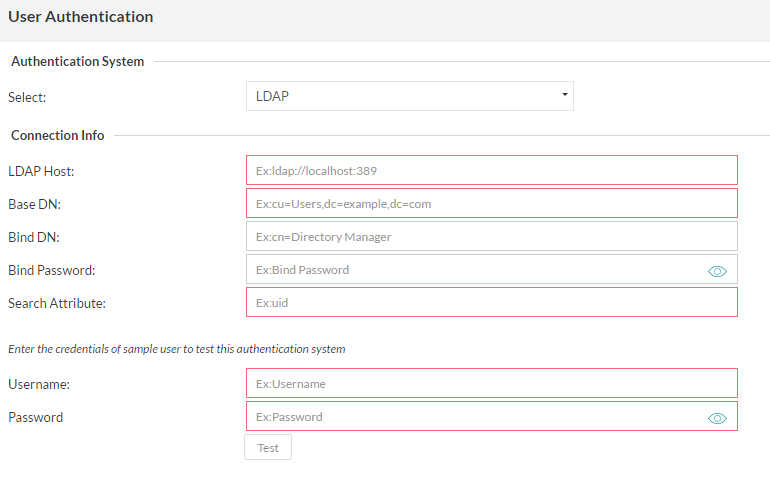
The LDAP authentication system in Zephyr allows an Administrator user the advantage of using a LDAP system to authenticate Zephyr users outside of Zephyr itself. Below are detailed descriptions of the fields in the LDAP authentication setup. LDAP Host [REQUIRED]: The IP address of your LDAP instance (default port 389). Currently does not support HTTPS.
BASE DN [REQUIRED]: Folder and Domain where the users will be that need authenticating.
BIND DN: Admin user, Folder, and Domain that will be used to search the other folders. This user/Directory Manager MUST have the ability to look through the domain for the users that need authenticating.
|
| Anchor | ||||
|---|---|---|---|---|
|
If your organization is using a Crowd server for authentication, the Zephyr Server can be setup to authenticate with Crowd before allowing users to log into the system.
After entering the relevant 'Connection Info', the authentication can be tested by entering the username and password of a user and clicking on the 'Test' button. This provides feedback on whether the authentication system was reachable and if the authentication was successful or a failure.
| Anchor | ||||
|---|---|---|---|---|
|
If your organization is using a different authentication system, then you could write a WebService that the Zephyr Server can call to authenticate against before allowing users to log into the system.
After entering the relevant 'Connection Info', the authentication can be tested by entering the username and password of a user and clicking on the 'Test' button. This provides feedback on whether the authentication system was reachable and if the authentication was successful or a failure.
5. Single Sign-On (SSO)Anchor SSO SSO
If your organization is using a Single Sign-On (SSO) for authentication, the Zephyr Server can be setup to authenticate with it before allowing users to log into the system.
...