| Table of Contents |
|---|
...
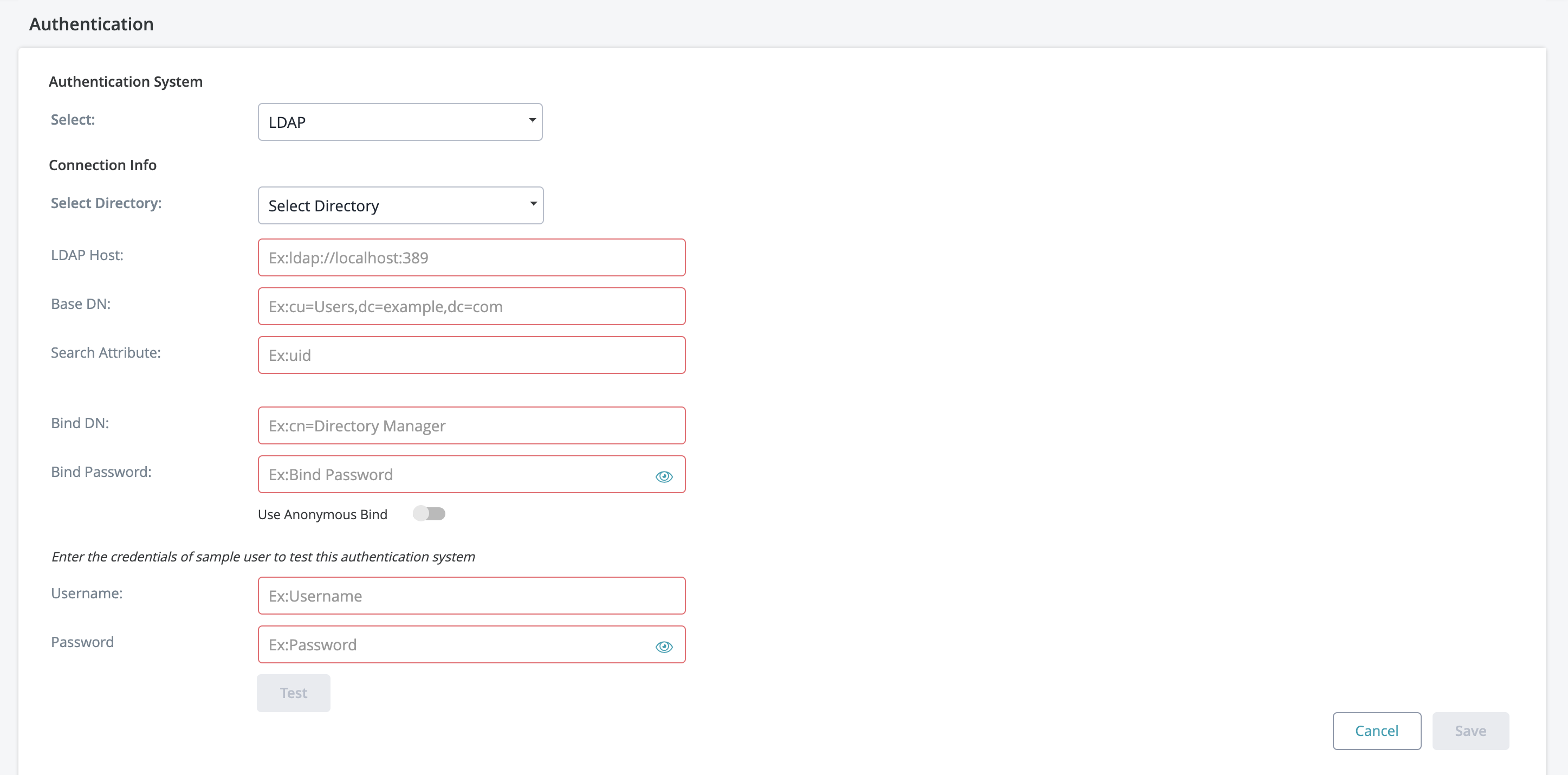
If your organization is using an LDAP server for authentication, the Zephyr server can be setup set up to authenticate users using LDAP.
...
Microsoft Active Directory
Apache Directory Server (ApacheDS)
OpenDS
OpenLDAP
A generic LDAP directory server
Both LDAP and LDAPS (secure LDAP) are supported.
LDAP Configuration
Connecting to an LDAP Directory in Jira
Select Administration.
Choose Authentication.
Add a directory and select one of these types:
'LDAP' – You will be able to choose a specific LDAP directory type on the next screen.
Enter the values for the settings, as described below.
Save the directory settings.
Server Settings
| Setting | Description |
|---|---|
| Directory Type | Select the type of LDAP directory that you will connect to. If you are adding a new LDAP connection, the value you select here will determine the default values for many of the options on the rest of the screen. Examples:
|
Hostname | Your LDAP server in the format
Note: If you use LDAPS (secure LDAP) and your LDAPS server uses a self-signed certificate, you need to configure Zephyr to trust this certificate. See the instructions below. |
| Base DN | The root distinguished name (DN) to use when running queries against the directory server. Examples:
For Microsoft Active Directory, specify the base DN in the following format: dc=domain1,dc=local. You will need to replace the domain1 and local for your specific configuration. Microsoft Server provides a tool called ldp.exe which is useful for finding out and configuring the the LDAP structure of your server. |
| BIND Bind DN | The distinguished name of the user that the application will use when connecting to the directory server. Examples:
|
| BIND Bind Password | The password of the user-specified above. |
| Search Attribute | The attribute field to use when loading the username. Examples:
|
Advance Settings
User Schema Settings
| Setting | Description |
|---|---|
| Search AttibuteAttribute | The attribute field to use when loading the username. Examples:
|
| User Object Class | This is the name of the class used for the LDAP user object. Example:
|
User Object Filter | The filter to use when searching user objects. Example:
|
| User First Name Attribute | The attribute field to use when loading the user's first name. Example:
|
User Last Name Attribute | The attribute field to use when loading the user's last name. Example:
|
| User Email Attribute | The attribute field to use when loading the user's email address. Example:
|
Group Schema Settings
| Setting | Description |
|---|---|
| Group Object Class | This is the name of the class used for the LDAP group object. Examples:
|
| Group Object Filter | The filter to use when searching for group objects. Example:
|
| Group Name Attribute | The attribute field to use when loading the group's name. Example:
|
| Group Description Attribute | The attribute field to use when loading the group's description. Example:
|
Membership Schema Settings
| Setting | Description |
|---|---|
Group Members Attribute | The attribute field to use when loading the group's members. Example:
|
| User Membership Attribute | The attribute field to use when loading the user's groups. Example:
|
Using LDAPS with a Self-Signed CertificateAnchor ldaps ldaps
| ldaps | |
| ldaps |
If your LDAPS server uses a self-signed certificate or a certificate signed by a private CA, you need to add it to the Java cacerts file on your Zephyr server. The cacerts file contains the trusted certificates.
To add your LDAPS certificate to cacerts, run the following command on your Zephyr server, replacing the paths with your own.
On Windows:
| Code Block | ||
|---|---|---|
| ||
keytool -importcert -alias "ldapsCer"
-keystore "C:\Program Files\Java\jre1.8.0_231\lib\security\cacerts"
-file "C:\Users\Administrator\Documents\ldapsCer.cer" |
Note: The line breaks above are added for readability. The entire command must be written on one line.
On Linux:
| Code Block | ||
|---|---|---|
| ||
keytool -importcert -alias "ldapsCer"
-keystore "/usr/java/jdk1.8.0_144/jre/lib/security/cacerts"
-file "/home/ldapsCer.cer" |
Anonymous Bind
When setting up your LDAP connection, we provide you with an option to connecting without requiring the BindDN Bind DN and BindPasswordBind Password. To connect to LDAP without requiring this information, simply enable the Anonymous Bind feature when setting up LDAP.
- Anonymous Bind is essentially an LDAP server function that allows the client to connect and search the directory (bind and search) without requiring the BindDN Bind DN and BindPasswordBind Password.
- To use Anonymous Bind, click on the checkbox to ensure it is enabled during the LDAP connection setup process.
Below the 'Connection Info' section there will be a place to test the connections and LDAP credentials used. This is useful for a quick check to see if everything is working. The username and password here can be a user in your directory that you wish to log on the Zephyr system with. Once the information is correct you can click the 'Test' button button and if everything goes correctly, you should see a 'Validation Successful!' popup. Otherwise, start troubleshooting the setup.
LDAP Required Fields
1. What are the required fields for connecting to LDAP?
- Open DS: LDAP Host, Base DN, and Search Attribute are required.
- The username and password for users who can authenticate are required.
- Active Directory: LDAP Host, Base DN, and Search Attribute.
- The username and password for users who can authenticate are required.
2. Is a unique Organizational Unit needed for Zephyr? (Organization Unit can be - Zephyr)
- The organizational unit can be any name. It does not necessarily have to be specific to Zephyr.
3. Is Bind DN required?
- Bind DN is required for Active Directory.
- Bind DN is not required for Open DS.
...